PEASS-ng, which stands for “Privilege Escalation Awesome Scripts SUITE new generation,” is a collection of applications that is mostly managed by Carlos Polop.
Enumeration tools are what PEASS-ng is known for, which makes sense given its name.
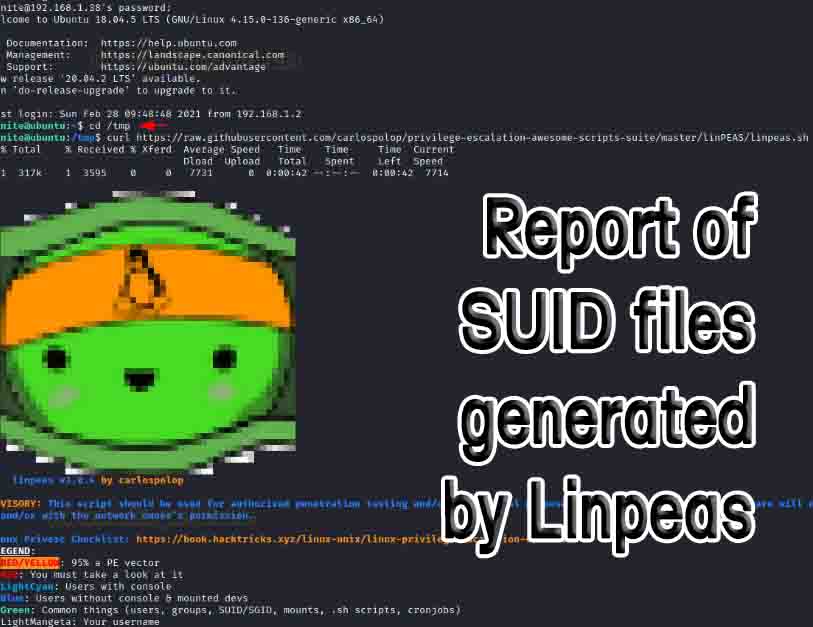
utilized in the process of elevating privileges. The situation in which an attacker gets access to a shell on the machine being targeted is ideally suited for their application because it is the most common one. The objective of the attacker is to achieve privileged escalation, either horizontally or vertically. In order to accomplish this, he runs the enumeration tool on the machine that is the target and checks the output of the tool. This output from the program displays a lot of information that could be helpful in locating privileged escalation paths, and it is displayed below.
This suite’s three most important applications are called WinPEAS, LinPEAS, and MacPEAS, and they correspond to the three most popular desktop operating systems (Windows, Linux and MacOS).
While LiPEAS and MacPEAS are identical, WinPEAS can be either an executable file or a batch file.
sh file that, when launched, automatically determines whether it is being executed on a machine running MacOS or Linux and then performs the appropriate tests for either operating system.
It would appear that the tools provided by PEASS-ng are tailor-made for our requirements; provided that a target computer has an interactive shell, all that is required of us is to upload the appropriate tool, run it, and check the vulnerability that it reports. The question then becomes: why didn’t we just develop a script that uploads WinPEAS or LinPEAS onto the system in question and then runs it?
The fact that WinPEAS and LinPEAS are not vulnerability assessment tools, but rather enumeration tools, is the primary source of the problem. This indicates that they do not only reveal the vulnerability that was discovered on the target computer; rather, in addition to that, they additionally report a large amount of information that is not immediately related to a particular vulnerability. Linpeas, for instance, will report on executable files that have the SUID permission set. This is not a vulnerability in and of itself; rather, it has the potential to become one if one of the files is owned by a privileged user and has the ability to be abused to run commands with elevated privileges. It is feasible to observe that a large number of files that do not contain a vulnerability are reported as containing a vulnerability.
Because of this behavior, the output of WinPEAS and LinPEAS is identical.
verbose for our needs, leaving the user with the repetitive effort of cleansing the reports from the worthless bits of the information they contain.
We did not include PEASS-ng since, in our opinion, it is not one of the most significant competitors. In point of fact, despite the fact that its tools have certain noteworthy features, we cannot consider them to be vulnerability assessment tools.
Protocols for interactive shell environments
Our vulnerability scanner is equipped with a Command-Line Interface (CLI), which it uses to issue commands to remote targets. Staresc makes use of some client libraries that are responsible for implementing interactive shell protocols in order to achieve access to these CLIs.
Telnet and SSH are the two protocols that are supported by Staresc, and in this section, we will cover both of them. Even if they are the most popular interactive shell protocols in a Unix-like environment and cover a large number of use-cases, we will demonstrate that Staresc is easily upgradable by adding support for additional protocols. This is the case even if they are the most popular interactive shell protocols in a Unix-like environment. This will remain the case despite the fact that they cover a very wide variety of applications.